Recently, I presented a talk on the main stage at BSides London 2024 and the topic I chose to present on was in regards to bringing trusted binaries to a system and using them in an adversarial fashion. This post will cover what I presented and how to use these binaries in detail. If you would also like a copy of the slides they can be found here. My talk was mainly focused on binaries that allow for the passing of the following 5 scenarios: Proxy my Kali tools, and tunnel traffic into an environment Bypass EDR (e.g. CrowdStrike), on dropping to disk and on execution Firewall friendly A good alternative to network tunnelling tools (e.g. Ligolo) Doesn't require a pre-installed SSH client The first solution is pictured below where the 'cloudflared' binary from, you guessed it, Cloudflare can be used in conjunction with the SSH 'ProxyCommand' to allow 'cloudflared' to transport the SSH...
JUMPSEC LABS
The JUMPSEC Lab is a place where the technical team get creative and showcase their latest security research, publications, interesting news and general thoughts! We love what we do and are passionate about security, with some great upcoming projects planned, bookmark our site and stick around to see what we are working on.
Building Forensic Expertise: A Two-Part Guide to Investigating a Malicious USB Device (Part 2)
In this part 2, we'll walk you through the step-by-step process of setting up and conducting a Digital Forensics and Incident Response (DFIR) investigation using a virtual...
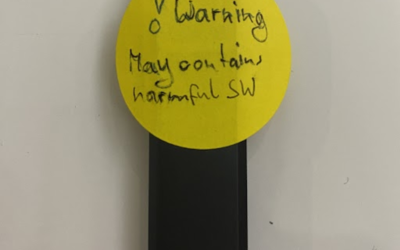
Building Forensic Expertise: A Two-Part Guide to Investigating a Malicious USB Device (Part 1)
JUMPSEC believes heavily in learning and developing through real world experience. The incident described in this blog post presented a fantastic opportunity for 3 junior team...
Obfuscating C2 During a Red Team Engagement
Command-and-Control (C2) infrastructure is one the most important tools in a red teamer’s arsenal. In this article, we introduce a few simple methods that red teams use to harden their C2 infrastructure.
PRINTNIGHTMARE NETWORK ANALYSIS
By Dray Agha The infosec community has been busy dissecting the PrintNightmare exploit. There are now variations of the exploit that can have various impacts on a target machine. When we at JUMPSEC saw that Lares had captured some network traffic of the PrintNightmare exploit in action, I wondered if there was an opportunity to gather network-level IoCs...
Securing against new offensive techniques abusing active directory certificate service
SpecterOps recently released an offensive security research paper that details techniques enabling an adversary to abuse insecure functionality in Active Directory Certificate Service. SpecterOps reports that abusing the legitimate functionality of Active Directory Certificate Service will allow an adversary to forge the elements of a certificate to authenticate as any user or administrator in...
Overcoming Issues Using Custom Python Scripts with Burp Suite Professional
Summary / TL:DR I recently encountered some issues when using Burp Suite Professional which led me to playing around with the Python Scripter extension. The extension allows running custom Python scripts on every request/response processed by Burp, including those generated by functionality such as Burp's active scanner. This has a number of potential use cases, but I found it particularly...
Win a place @HackFu 2021 Community Edition!
Hello world!At JUMPSEC we’ve managed to get our hands on tickets to what is probably the greatest cyber security event in the calendar, HackFu!In order to be in with a chance of winning you simply need to complete the following challenge which you can download here (the download contains all the information needed to complete the challenge):...
Detecting known DLL hijacking and named pipe token impersonation attacks with Sysmon
Recently we posted a bunch of advisories relating to Ivanti Unified Endpoint Manager, a couple of which are for vulnerabilities which can be used to achieve local privilege escalation. We will give a brief explanation of the vulnerabilities and an example of Sysmon configuration rules to log exploitation attempts, along with the rationale behind them so you can adapt them to your existing configuration if needed.
Advisory CVE-2020-13773 – Ivanti Unified Endpoint Manager Reflected XSS
Software: Ivanti Endpoint ManagerAffected Versions: <= 2020.1.1Vendor page: www.ivanti.comCVE Reference: CVE-2020-13773Published: 13/11/2020CVSS 3.1 Score: 5.5 - AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:L/A:LAttack Vector: Remote, authenticatedCredits: Andrei Constantin Scutariu, Lenk Ratchakrit, Calvin Yau Summary Various web pages on Ivanti Unified Endpoint Manager web management console lack proper...
Advisory CVE-2020-13769 – Ivanti Unified Endpoint Manager SQL injection
A number of web components in Endpoint Manager do not properly sanitize user input when executing SQL queries, leaving the application vulnerable to injection attacks towards the underlying database. On a standard installation with default options, the account used to query the database is database administrator.
Disclaimer
The information provided on this website is to be used for educational purposes only. The author is in no way responsible for any misuse of the information provided. Any actions and or activities related to the material contained within this website is solely your responsibility.