JUMPSEC’s Detection and Response Team (DART) responds to many phishing threats targeting our clients. An interesting incident I recently had to respond to, was a critical alert titled "multi-stage alert involving Initial Access & Lateral Movement". This alert was triggered by a series of phishing emails targeting individuals with lures presenting a common theme. In this LABS post, I’ll walk you through the investigation, how we pieced together several bits of information to figure out the tactics and infrastructure used by the attackers, and the steps taken to mitigate the threat. Incident Overview Microsoft Defender XDR (eXtended Detection and Response) triggered the alert that four emails matched our alert policy relating to “malicious URL that were delivered and later removed”. Using the “Email Preview” feature in Defender, I was able to see that all the phishing emails shared a...
JUMPSEC LABS
The JUMPSEC Lab is a place where the technical team get creative and showcase their latest security research, publications, interesting news and general thoughts! We love what we do and are passionate about security, with some great upcoming projects planned, bookmark our site and stick around to see what we are working on.
Please Mind the CAP – Modern Conditional Access Policy circumvention and what it means for your organisation (webinar recording)
Webinar recording -...
Bring Your Own Trusted Binary (BYOTB) – BSides Edition
Recently, I presented a talk on the main stage at BSides London 2024 and the topic I chose to present on was in regards to bringing trusted binaries to a system and using them in...
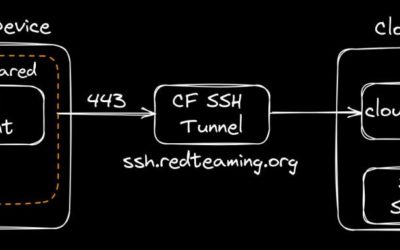
Putting the C2 in C2loudflare
tl;dr How to bring up an entire C2 infrastructure with all your tooling and their corresponding redirectors within 5 minutes with the help of Azure Snapshots, Cloudflare and Tmux Resurrect. Every so often I seem to stumble across various ideas, that when combined, massively improve my overall productivity at work. Most of these ideas on their own are nothing new, but when used in tandem can...
Bullet Proofing Your Email Gateway
In this labs post, I will introduce you to modern security controls that are currently used (but not always correctly) by the vast majority of enterprises, and hopefully by the end of this write-up, the topic will become a little clearer and the concepts will become easier to grasp. In today’s world of spammers, intruders, and fake emails, having a robust setup for your email deliveries is...
What’s in a Name? Writing custom DNS tunnelling protocol, exploiting unexpected AWS Lambda misconfiguration – in a web app Pen test (Part 2)
In Part 1 of the series we looked at how an AWS Lambda-powered feature was exploited in a web app penetration test initially leading to RCE and further on with out-of-band data exfiltration via DNS. Though the exact mechanism of achieving remote-code execution with Python was not discussed, we went in depth in how to return data as a result of the code being executed. Initially, with...
What’s in a Name? Writing custom DNS tunnelling protocol, exploiting unexpected AWS Lambda misconfiguration – in a web app Pen test (Part 1)
This is a war story of an AWS web application test where remote code execution was first obtained on the client's application. Then I needed to write my own DNS tunnelling 'protocol' to get the data out. Following a number of twists and turns I impersonated the application and attempted to laterally move within the AWS tenant. Before storytelling though, let's start with a public service...
WASM Smuggling for Initial Access and W.A.L.K. Tool Release
TL;DR This blog post introduces Web Assembly (WASM) as a powerful alternative to traditional web technologies, highlighting its appeal to cybersecurity professionals for evading security measures for initial access. WASM has been observed being leveraged in the wild as a new payload delivery avenue which can land payloads in a hardened email inbox or instant messaging chats. A new tool, W.A.L.K....
Adventures and Accidental Honeypots in Network Infrastructure: Unravelling Internet Shenanigans
Hello World! So, I've been tinkering with network stuff lately, trying to set up some infrastructure.Turns out that in the process, I made a rookie mistake and left a few ports open to the internet! A few months down the line I took a look and to no one’s surprise my server had been bombarded with all sorts of requests. It was receiving a steady stream of traffic, but not the good kind…think of...
Poisoning Pipelines: Azure DevOps Edition
Introduction In the ever-evolving realm of cloud services, organisations are ditching the headaches of physical infrastructure management and diving headfirst into the possibilities of cloud platforms. From the humble beginnings of deploying virtual machines and servers, we now find ourselves in a dynamic space with everything from serverless architectures to cloud-based active directories,...
Why sneak when you can walk through the front door – A Love letter to Password Spraying against M365 in Red Team Engagements
In 2023 through 2024, JUMPSEC's red team gained access to Microsft 365 (M365) environments of sophisticated clients during adversarial engagements with an approach that breathes life into the decades-old technique of password spraying. With threat actors increasingly using similar approaches in the wild, being able to compromise the even likes of Microsoft themselves, it is my opinion that red...
Disclaimer
The information provided on this website is to be used for educational purposes only. The author is in no way responsible for any misuse of the information provided. Any actions and or activities related to the material contained within this website is solely your responsibility.